
San Francisco, California, United States
Tinfoil makes your AI workflows secure, verifiable, and private.
- Revenue
- $660K
- Customers
- -
- Year founded
- 2024
- Funding
- -
- Team size
- 6
- Growth
- -
As of May 2026, there are 9 SaaS companies in Confidentiality Software. They have combined revenues of $14.3M and employ 96 people. They have raised - and serve 1.8K customers combined.
Confidentiality software is designed to protect sensitive information and ensure that data remains confidential throughout its lifecycle. It serves various industries, particularly those dealing with regulated information such as finance, healthcare, and government, by implementing strong security measures to safeguard data from unauthorized access and breaches. The primary use cases for confidentiality software include securing data at rest, in transit, and in use through advanced encryption techniques and secure environments. Typical features may consist of access controls, audit trails, secure data sharing, and compliance tracking with applicable regulations. Buyers of confidentiality software often include IT security professionals, compliance officers, and risk management teams, who prioritize data privacy and protection in their operations.
Sorting: Highest -> Lowest
Showing 10 of 4 companies ranked by annual revenue.

San Francisco, California, United States
Tinfoil makes your AI workflows secure, verifiable, and private.

Brooklyn, New York, United States
Sanctum is a private AI application that runs full-featured, open-source LLMs locally. Chat with AI, interact with documents, and keep your data encrypted, ensuring it never leaves your device.
Chihuahua, Chihuahua, Mexico
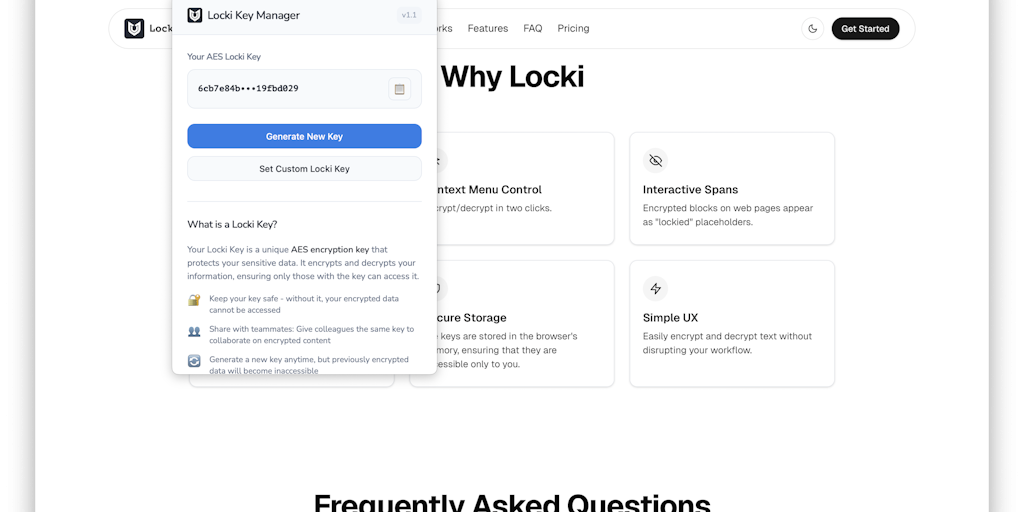
Locki is a lightweight browser extension that makes it simple to protect your sensitive data. It automatically encrypts text before sending it and decrypts it when received, keeping your communication private and secure.
- Must provide encryption for data at rest, in transit, and in use. - Should include role-based access controls to restrict user access based on permissions. - Must offer auditing features to track data access and modifications. - Should comply with relevant data protection regulations and standards. - Not just a tool for securing single data points; must also provide comprehensive data lifecycle management. - Must integrate with existing IT infrastructure to enhance security posture without extensive overhauls.
Each Tuesday, we reverse-engineer a real SaaS company's revenue, profit, CAC, funnels, and its top growth tactic.
Sign up to access all features
Sign up with GoogleSign up with LinkedInAlready have an account? Log in
GetLatka is trusted by 200k+ founders, researchers, and marketers.
No contracts, cancel at any time